Cyber Security Threats to the Food Industry: Consider the Cloud
By Roger Woehl
With growing news reports of cyber security and foreign hackers, it makes one think: Are US food companies at risk for cyber-attack?
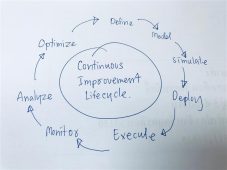
In many ways, the risks from cyber threats are no different than the safety risks that food companies mitigate every day. The same practices used to identify and address food-processing risks, such as foreign materials and pathogens, can apply to protecting data essential for processing. These practices call for evaluating the threats, assessing the likelihood of occurrences, and establishing programs for mitigation.
The security risks to food data fall into a few categories: theft, public exposure, data corruption or loss, and data manipulation or falsification. Assessing the likelihood of attack in each category requires identifying malicious actors and how each might benefit from an attack. Is the actor a foreign agent, cybercriminal, disgruntled employee, a competitive spy, or extremist food activist? How would a bad actor benefit from stealing, exposing, manipulating, or corrupting data?
An inability to show a HACCP check could result in millions of dollars lost in product recall or disposal.
Low Threat of Theft
The threat of theft is low. Unlike personal private data contained in financial or HR systems, manufacturing data has low value. Certainly, companies with proprietary formulas or processes must protect this from foreign counterfeiters. A viable scenario for safety and quality data theft takes on the characteristics of a near Hollywood-type plot: “Zealous food activists hack corporate data to expose the evils of big food” – an unlikely occurrence.
While theft risks are low, others are much higher. Data corruption or loss could result in significant financial impact. An inability to show a HACCP check could result in millions of dollars lost in product recall or disposal. These financial risks make this data a target for criminal hijackers who can encrypt data and hold it hostage for a ransom. This is known as a “ransomware” attack and is a growing cyber security threat. According to Newsweek, ransomware attacks increased by over 250% in 2017 compared with 2016. For example, the “NotPetay” attack impacted multiple firms in the US, including pharmaceutical giant Merck, which paid out more than $300 million in Q3 of 2017 to recover data.
Once risks are assessed, a data security program can be established with practices similar to those that ensure safe, quality products. Data security professionals will call for familiar actions like:
- maintaining zones of security to prevent threat migration
- protecting and monitoring critical control points and
- conducting regular tests of risk points and the general environment.
Security zones are an essential first step. Just as you would isolate raw incoming materials from cooked and processed materials, you must do the same with data. If operational data resides on the same network as employee computers and email, then risks are high that an email virus could impact company data. Keeping sensitive data isolated minimizes access points.
Managing control points requires securing access from data ports to user accounts. These basic practices are as essential to data security as hand washing and hairnets are to food safety.
Implementing Deep Security
Done independently, implementing deep security can be a considerable expense, requiring expertise, hardware, training, and continuous diligence. One surprising cost-effective method for protecting data is transitioning from an on-premises system to a cloud-based Food Quality Management system. This approach may seem counterintuitive on the surface; however, cloud-based data companies are the most well-equipped to protect data. Cloud-based companies are hyper-focused on data security because their business’ health depends it. Cloud-based companies have resources such as security experts, backups, redundancy, testing, monitoring, and other practices that are cost-prohibitive for individual companies.
Cyber threats are a growing reality in today’s business climate. Fortunately, the safety culture engrained in the US food industry makes it well-equipped to manage these risks, and new approaches, like cloud-based food quality management software, are providing cost-effective ways to stay a step ahead of the bad actors.
About the Author
Roger Woehl is Chief Technical Officer at SafetyChain Software, Inc. and has over 20 years’ experience developing innovative B2B SaaS solutions. Past roles include VP of HR, Talent Management and Enterprise portal solutions at Infor and CTO at Enwisen, the HR industry’s leading SaaS portal solution serving Fortune 500 companies. Roger has a BS in Mechanical Engineering and 10 patents including software and aerospace electrical interconnect design.

-
 FeaturedRisk management
The Cost of a Breach: What a Cyberattack Could Mean for Food Safety Recalls
FeaturedRisk management
The Cost of a Breach: What a Cyberattack Could Mean for Food Safety Recalls
-
 FeaturedRisk management
Securing the Food Chain: How ISO/IEC 27001 Strengthens Cybersecurity
FeaturedRisk management
Securing the Food Chain: How ISO/IEC 27001 Strengthens Cybersecurity
-
 FeaturedRisk management
Revolutionizing Food Safety Training: Breaking Out of the “Check-the-Box” Mentality
FeaturedRisk management
Revolutionizing Food Safety Training: Breaking Out of the “Check-the-Box” Mentality
-
 GFSI Standards
GFSI 2025: Building Trust, Tech-Forward Solutions, and Global Unity in Food Safety
GFSI Standards
GFSI 2025: Building Trust, Tech-Forward Solutions, and Global Unity in Food Safety
-
 FeaturedFood Safety
Integrated Pest Management: Strategies to Protect Your Brand’s Reputation
FeaturedFood Safety
Integrated Pest Management: Strategies to Protect Your Brand’s Reputation
-
 FeaturedFood Safety Culture & Training
No Open Door Policy: Challenges That Impact Pest Control in Food Processing Plants
FeaturedFood Safety Culture & Training
No Open Door Policy: Challenges That Impact Pest Control in Food Processing Plants




