Communication: Your Cyber Crime Fighting Secret
By Linda Eatherton
Cybercrime threatens every operating organization. Data thieves and trolls lurk in cyberspace waiting for an opportunity to attack, and pose the type of threat that, from a food safety perspective, can be exceptionally damaging. Cyber attacks deploy faster, more widely and more credibly than any threat ever experienced by businesses before.
The PWC Economic Crime and Fraud Survey 2022, a study conducted among 1,296 executives in 53 countries and regions, indicates more than half of respondents experienced fraud in the past two years – the highest level reported in the survey’s 20-year history.
Half of those businesses reporting cybercrimes lost one million dollars or more as a result of the attack. In reality, we know that billions of dollars have been lost by corporations unwilling to share their painful experiences. Forbes estimates that ransomware costs alone will reach $265 billion by 2031.
Cybercrime and data breaches are no longer exceptional events. Every business must prepare for the eventuality that it will experience tech disruption and damage at some point.
Cybercrime and data breaches are no longer exceptional events. Every business must prepare for the eventuality that it will experience tech disruption and damage at some point. The more we rely upon technology, the more risk it presents. In the case of cybercrime, it’s now a matter of when, not if, your company will be targeted.
As with any crisis, communication plays a critical role in both preparing for and managing through the worst of times. Communication is also the foundation upon which we build valued relationships. Cybercrime attacks those critical relationships, making it one of the most deadly threats to the corporate brand. The massive disruption in communication during and long after the digital event can break the bond of trust between your brand and your stakeholders.
A cyberbreach is one of the few crisis situations that prompts a total information blackout between the organization, and every person and company it deals with. Servers are compromised. Files are seized. Email accounts are frozen. All social and digital communication channels are rendered temporarily useless. In the darkness, fear and speculation take hold.
Trust, once broken, is exceptionally difficult to repair. For this reason, communications professionals need to take a central role within senior management, risk management and crisis planning. You can reboot systems, but you can’t reboot trust overnight. This is especially true when it comes to protecting the science, technology and information others rely upon to support human health.
Some companies view communications as the ‘clean-up crew’ responsible for damage control. This outdated thinking can hamper recovery as it relates to cybersecurity issues. No PR campaign can reverse the reputational damage that has been done. A company’s actions are the most effective means to rebuild trust. Communication provides the vehicle for sharing those actions with stakeholders
Today’s communications professionals should be viewed as the ‘keepers of confidence’ instead of the ‘clean-up squad’. Communicators can deploy an arsenal of tools to build, restore and protect stakeholder confidence.
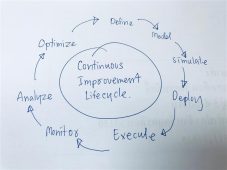
There are proactive steps communicators can take to combat cybersecurity challenges:
Elevate and Merge Risk Management and Crisis Planning
Cybersecurity issues come in a wide variety of situations from malware to ransomware. All potential cybersecurity situations must be planned for with test scenarios run in advance. No two are alike. A ransomware situation instantly puts your CEO into the position of deciding how and what you will pay to retrieve your data.
Plan for the Worst and Simulate Responses
The opportunity for and incidence of cyber attacks escalated during the pandemic resulting from the remote workforce. “Lack of proximity, working from home, remote systems gave them room to move in,” said Reena Bajowala, partner and cybersecurity lawyer with Ice Miller Law Firm in a podcast. “And, the professionalization of ransomware has increased into a bona fide business where ‘experts’ develop malware variants to lock up data; perfecting and customizing it each time.”
Ensure that top leadership and the heads of all key internal functions plan and drill with external cyber and data security lawyers, forensic consultants and systems experts to prepare for potential attacks. Practice full-on cyberattack simulations to ensure the organization can activate contingency plans immediately, and employees have clarity on their roles within the process. Stress test back-up systems to determine how much data can be recovered and how fast.
Align and Design to Disclose
Because trust and human safety hang in the balance, it is critical that the organization aligns in advance on who will communicate with which audiences, in what order, and at what intervals. There are a wide range of legal and contractual terms that dictate specific disclosures; each with different requirements. Disclosure is generally non-negotiable and predetermined. These should be summarized in advance as part of the core crisis response plan. “There are 54 data breach notification laws in this country alone and they all have … different tests for when they trigger notification. Most have some variation of ‘notify as expediently as possible,’ says Bajowala.
Study after study, situation after situation, tell you it is best to disclose ‘as a precaution’ even before you know who and what is affected. The alert, while concerning, allows your stakeholders to take security precautions and heighten monitoring. Nothing is more damaging to relationships and trust than to receive a notification six months after the fact. Creating multiple stand-by statements to alert and update key audiences is time well-spent in planning. This can’t be left to the last minute when seconds count and tensions are high.
Remember, email accounts may all be tied up indefinitely. In that event, how will you reach employees, customers, or key partners to give them a head’s up? Where is contact information stored? Is it current? How will you monitor what is being shared on social media? In the mainstream press? No amount of goodwill can override a breach if you have no viable communication channels available to share your story.
Monitor and Manage Always be on high alert.
Your data surveillance systems should be working as hard as your digital communications surveillance systems. Track what people are saying on various media platforms. Be uber-aware of conversations that could be early warning signals you are about to be attacked. For example, when JBS, an international meat processing company, was held hostage by cyberattackers this news should have alerted other meat and fresh food processors that they were possibly only minutes away from a similar attack. Creating and maintaining trust is the most crucial part of our work to promote and support health and human safety. While many attempts to dismantle that trust are inevitable, communicators can insulate the brand and the business from irreparable breaks of confidence through preparation and proactive measures.
Stay ahead with the latest in Food Safety! Free subscription, unlimited access. Sign up now!
About the Author:
Linda Eatherton, president, and founder of Eatherton Consulting, designs leading-edge communications strategies that help food innovators and renovators build and protect their brands, businesses and IP. Her entire career has been spent in service to the food and agricultural space. Prior to consulting, she led the highly regarded global F&B practice at Ketchum, where she directed more than 300 individuals worldwide, solving reputational issues, marketing branded products and ingredients and strengthening stakeholder relationships for both supply and value chain organizations.

-
 FeaturedRisk management
The Cost of a Breach: What a Cyberattack Could Mean for Food Safety Recalls
FeaturedRisk management
The Cost of a Breach: What a Cyberattack Could Mean for Food Safety Recalls
-
 FeaturedRisk management
Securing the Food Chain: How ISO/IEC 27001 Strengthens Cybersecurity
FeaturedRisk management
Securing the Food Chain: How ISO/IEC 27001 Strengthens Cybersecurity
-
 FeaturedRisk management
Revolutionizing Food Safety Training: Breaking Out of the “Check-the-Box” Mentality
FeaturedRisk management
Revolutionizing Food Safety Training: Breaking Out of the “Check-the-Box” Mentality
-
 GFSI Standards
GFSI 2025: Building Trust, Tech-Forward Solutions, and Global Unity in Food Safety
GFSI Standards
GFSI 2025: Building Trust, Tech-Forward Solutions, and Global Unity in Food Safety
-
 FeaturedFood Safety
Integrated Pest Management: Strategies to Protect Your Brand’s Reputation
FeaturedFood Safety
Integrated Pest Management: Strategies to Protect Your Brand’s Reputation
-
 FeaturedFood Safety Culture & Training
No Open Door Policy: Challenges That Impact Pest Control in Food Processing Plants
FeaturedFood Safety Culture & Training
No Open Door Policy: Challenges That Impact Pest Control in Food Processing Plants




